Introduction
SSH is an acronym for Secure Shell. Secure Shell is a network protocol which basically means a set of rules and guidelines that tells your computer how to send information from one place to another.
What is SSH?
SSH(like FTP) can be used for transmitting data, commands from one place to another and for transmitting files. It can be used on a variety of computers and on various platforms.
The most visible application of the protocol is for access to shell accounts on Unix like operating systems but it sees some limited use on windows as well.
The encryption used by SSH is intended to provide confidentiality and security of data while transmitting private and confidential information blocking the interference caused otherwise midway.
Usage of SSH
SSH client program is typically used for establishing connections to an SSH daemon accepting remote connections. Most of the commonly present modern operating systems include OpenBSD, GNU/LINUX. Windows is one of the few modern server operating system that does not include SSH by default.
SSH is useful in cloud computing to solve connectivity problems, avoiding the security issues of exposing a cloud based virtual machine directly on the internet. An SSH tunnel can provide a secure path over internet through a firewall to a virtual machine.
It becomes handy in logging in to a remote machine and executing commands. Besides this it supports tunneling, forwarding TCP ports and X11 connections.
SSH Keys
An SSH key allows us to establish a secure connection between computer and server. They provide a more secure way of logging into a private server with SSH than using a password alone. The SSH keys offer high security as because it is nearly impossible to decipher them whereas a password on the other hand is more vulnerable.
Deploy keys
Deploy keys allow read-only access to multiple projects with a single SSH key.
This is really useful for cloning repositories to your Continuous Integration (CI) server. By using deploy keys, you don’t have to setup a dummy user account.
If you are a project master or owner, you can add a deploy key in the project settings under the section ‘Deploy Keys’. Press the ‘New Deploy Key’ button and upload a public SSH key. After this, the machine that uses the corresponding private key has read-only access to the project.
Generating a key pair provides you with two long string of characters.
◈ Public key
◈ Private key
Public key can be placed on any server and can then be unlocked by connecting it with the private key already present with the client.
By protecting the private key with a passphrase the security level can be considerably increased.
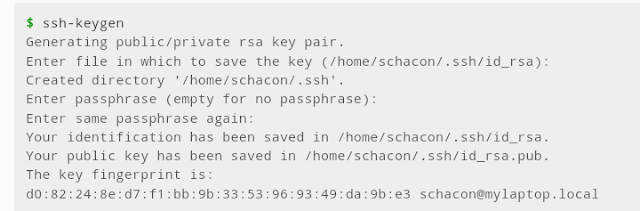
◈ Create RSA key pair
◈ Store keys and passphrase
◈ Copy public key
◈ Disable password
◈ Enhancements
These are intended for performance enhancements of SSH products:
◈ SSH-over-SCTP: support for SCTP rather than TCP
◈ ECDSA: support for elliptic curve DSA rather than RSA
◈ ECDH: support for elliptic curve diffie-hellman rather than plain diffie-hellman
◈ UMAC: support for UMAC rather than HMAC for MAC.








0 comments:
Post a Comment